Find MalOps for a Specific Machine
Sometimes, if you find that a specific machine has been compromised, you may want to find with what other malicious activity the machine is associated. In this case, you can return a list of MalOps for a specific machine.
Follow these steps to search for MalOps:
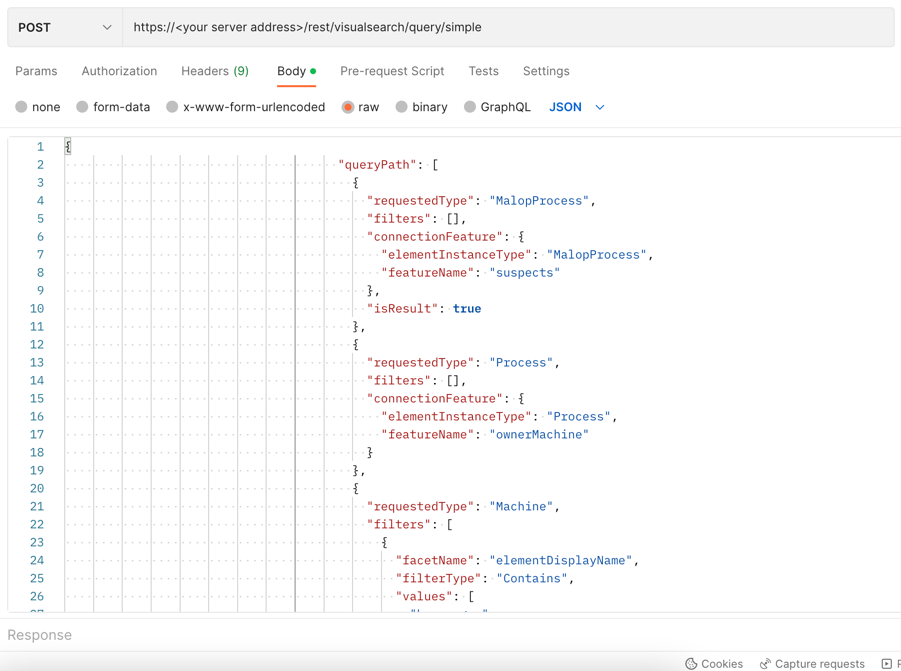
Step 1: Build the request to retrieve MalOps
To help you identify the MalOps for a machine, you need to build a query that filters by the machine name.
For this example, we will use the machine name hrmanager
To build the request, replace the placeholders in the relevant cURL command, request body example, or Python script:
curl --request POST \
--url https://<your server>/rest/visualsearch/query/simple \
--header 'Content-Type:application/json' \
--data '{
"queryPath": [
{
"requestedType": "MalopProcess",
"filters": [],
"connectionFeature": {
"elementInstanceType": "MalopProcess",
"featureName": "suspects"
},
"isResult": true
},
{
"requestedType": "Process",
"filters": [],
"connectionFeature": {
"elementInstanceType": "Process",
"featureName": "ownerMachine"
}
},
{
"requestedType": "Machine",
"filters": [
{
"facetName": "elementDisplayName",
"filterType": "Contains",
"values": [
"hrmanager"
]
}
],
"isResult": false
}
],
"totalResultLimit": "100",
"perGroupLimit": 1200,
"perFeatureLimit": 1200,
"templateContext": "DETAILS",
"queryTimeout": null,
"customFields": [
"elementDisplayName"
]
}'
Depending on your browser settings, this linked file may open in a separate tab instead of downloading directly to your machine. If this happens, use the Save As option in your browser to save the file locally.
{
"queryPath": [
{
"requestedType": "MalopProcess",
"filters": [],
"connectionFeature": {
"elementInstanceType": "MalopProcess",
"featureName": "suspects"
},
"isResult": true
},
{
"requestedType": "Process",
"filters": [],
"connectionFeature": {
"elementInstanceType": "Process",
"featureName": "ownerMachine"
}
},
{
"requestedType": "Machine",
"filters": [
{
"facetName": "elementDisplayName",
"filterType": "Contains",
"values": [
"hrmanager"
]
}
],
"isResult": false
}
],
"totalResultLimit": "100",
"perGroupLimit": 1200,
"perFeatureLimit": 1200,
"templateContext": "DETAILS",
"queryTimeout": null,
"customFields": [
"elementDisplayName"
]
}
Note
The code in this sample is repeated in the samples below. You do not need to run the script now but it is used here to help you understand how you build the request.
All Python examples are formatted for Python version 3.0 and higher, up to the latest Python version. If you are using versions of Python earlier than 3.0, ensure you manually remove parentheses for the print statements in this sample. For example, the print (response.content) statement updates to print response.content.
Depending on your browser settings, this linked file may open in a separate tab instead of downloading directly to your machine. If this happens, use the Save As option in your browser to save the file locally.
import requests
import json
# Login information
username = "[email protected]"
password = "mypassword"
server = "myserver.com"
port = "443"
data = {
"username": username,
"password": password
}
headers = {"Content-Type": "application/json"}
base_url = "https://" + server + ":" + port
login_url = base_url + "/login.html"
session = requests.session()
login_response = session.post(login_url, data=data, verify=True)
print (login_response.status_code)
print (session.cookies.items())
# Request URL
endpoint_url = "/rest/visualsearch/query/simple"
api_url = base_url + endpoint_url
# These are the variables that represent different fields in the request.
machine_name = "hrmanager"
query = json.dumps({"queryPath":[{"requestedType": "MalopProcess","filters":[],"connectionFeature":{"elementInstanceType":"MalopProcess","featureName":"suspects"},"isResult":True},{"requestedType":"Process","filters":[],"connectionFeature":{"elementInstanceType":"Process","featureName": "ownerMachine"}},{"requestedType": "Machine","filters":[{"facetName": "elementDisplayName","filterType": "Contains","values":[machine_name]}],"isResult":False}],"totalResultLimit": "100","perGroupLimit": 1200,"perFeatureLimit": 1200,"templateContext":s"SPECIFIC","queryTimeout": null,"customFields":["elementDisplayName"]})
api_headers = {'Content-Type':'application/json'}
api_response = session.request("POST", api_url, data=query, headers=api_headers)
your_response = json.loads(api_response.content)
print(json.dumps(your_response, indent=4, sort_keys=True))
Step 2: Run your request and generate the response
In the command line, REST API client, or IDE, run the command or script that contains the request. After a few seconds, the Cybereason API returns a response.
Step 3: Evaluate the response
The response contains a large number fields. Focus on these fields for meaningful information:
Example
{
"data": {
"resultIdToElementDataMap": {
"AAAA1kFkoAiE4Tf9": {
"simpleValues": {
"elementDisplayName": {
"totalValues": 1,
"values": [
""
]
}
},
"elementValues": {},
"suspicions": {},
"filterData": {
"sortInGroupValue": "",
"groupByValue": ""
},
"isMalicious": false,
"suspicionCount": 0,
"guidString": "AAAA1kFkoAiE4Tf9",
"labelsIds": null,
"malopPriority": null,
"suspect": false,
"malicious": false
}
},
"suspicionsMap": {},
"evidenceMap": {},
"totalResults": 1,
"totalPossibleResults": 1,
"guessedPossibleResults": 1,
"queryLimits": {
"totalResultLimit": 100,
"perGroupLimit": 100,
"perFeatureLimit": 100,
"groupingFeature": {
"elementInstanceType": "MalopDetectionEvents",
"featureName": "self"
},
"sortInGroupFeature": null
},
"queryTerminated": false,
"pathResultCounts": [
{
"featureDescriptor": {
"elementInstanceType": "MalopDetectionEvents",
"featureName": null
},
"count": 1
}
],
"guids": [
"AAAA1kFkoAiE4Tf9"
],
"paginationToken": null,
"executionUUID": "23505f1c-c6c2-42a9-8bc5-ab3a1f4137e4",
"quapiMeasurementData": {
"timeToGetGuids": [
67
],
"timeToGetData": [
24
],
"timeToGetAdditionalData": [
0
],
"totalQuapiQueryTime": [
93
],
"startTime": [
1682008688827
],
"endTime": [
1682008688921
]
}
},
"status": "SUCCESS",
"hidePartialSuccess": false,
"message": "",
"expectedResults": 0,
"failures": 0,
"failedServersInfo": null
}