Find Attackers Performing Reconnaissance
Use the API to find examples of an attacker performing reconnaissance on your systems.
The example queries in this section are meant to be a starting point for your investigations. You may need to update the Features (filters) in each query to use indicators specific to your environment or situation.
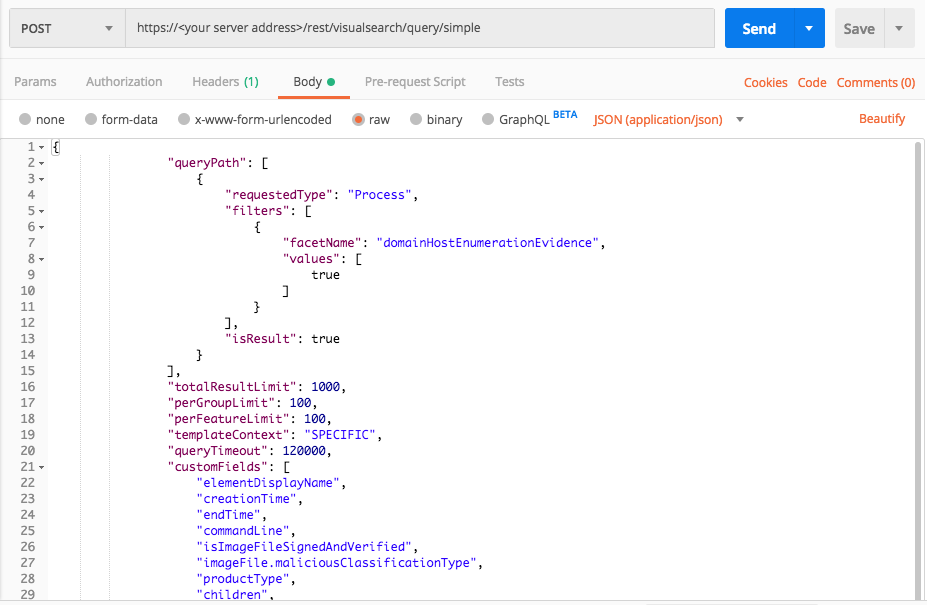
Host enumeration
Use this query to find evidence of a process trying to perform host enumeration and learn more about the domain host.
Request
curl --request POST \
--url https://12.34.56.78/rest/visualsearch/query/simple \
--header 'Content-Type: application/json' \
--data '{
"queryPath":[
{
"requestedType":"Process",
"filters":[
{
"facetName":"domainHostEnumerationEvidence",
"values":[true]
}
],
"isResult":true
}
],
"totalResultLimit":1000,
"perGroupLimit":100,
"perFeatureLimit":100,
"templateContext":"SPECIFIC",
"queryTimeout":120000,
"customFields":[
"elementDisplayName",
"creationTime",
"endTime",
"commandLine",
"isImageFileSignedAndVerified",
"imageFile.maliciousClassificationType",
"productType",
"children",
"parentProcess",
"ownerMachine",
"calculatedUser",
"imageFile",
"imageFile.sha1String",
"imageFile.md5String",
"imageFile.companyName",
"imageFile.productName",
"iconBase64",
"ransomwareAutoRemediationSuspended",
"executionPrevented",
"isWhiteListClassification",
"matchedWhiteListRuleIds"
]
}'
Request
Depending on your browser settings, this linked file may open in a separate tab instead of downloading directly to your machine. If this happens, use the Save As option in your browser to save the file locally.
Use this request body:
{ "queryPath": [ { "requestedType": "Process", "filters": [ { "facetName": "domainHostEnumerationEvidence", "values": [ true ] } ], "isResult": true } ], "totalResultLimit": 1000, "perGroupLimit": 100, "perFeatureLimit": 100, "templateContext": "SPECIFIC", "queryTimeout": 120000, "customFields": [ "elementDisplayName", "creationTime", "endTime", "commandLine", "isImageFileSignedAndVerified", "imageFile.maliciousClassificationType", "productType", "children", "parentProcess", "ownerMachine", "calculatedUser", "imageFile", "imageFile.sha1String", "imageFile.md5String", "imageFile.companyName", "imageFile.productName", "iconBase64", "ransomwareAutoRemediationSuspended", "executionPrevented", "isWhiteListClassification", "matchedWhiteListRuleIds" ] }
Request
Depending on your browser settings, this linked file may open in a separate tab instead of downloading directly to your machine. If this happens, use the Save As option in your browser to save the file locally.
import requests import json # Login information username = "[email protected]" password = "mypassword" server = "yourserver.com" port = "443" data = { "username": username, "password": password } headers = {"Content-Type": "application/json"} base_url = "https://" + server + ":" + port login_url = base_url + "/login.html" session = requests.session() login_response = session.post(login_url, data=data, verify=True) print (login_response.status_code) print (session.cookies.items()) # Request URL endpoint_url = "/rest/visualsearch/query/simple" api_url = base_url + endpoint_url # These are the variables that represent different fields in the request. query_element_1 = "Process" query_element_1_filter = "domainHostEnumerationEvidence" query = json.dumps({"queryPath":[{"requestedType":query_element_1,"filters":[{"facetName":query_element_1_filter,"values":[True]}],"isResult":True}],"totalResultLimit":1000,"perGroupLimit":100,"perFeatureLimit":100,"templateContext":"SPECIFIC","queryTimeout":120000,"customFields":["elementDisplayName","creationTime","endTime","commandLine","isImageFileSignedAndVerified","imageFile.maliciousClassificationType","productType","children","parentProcess","ownerMachine","calculatedUser","imageFile","imageFile.sha1String","imageFile.md5String","imageFile.companyName","imageFile.productName","iconBase64","ransomwareAutoRemediationSuspended","executionPrevented","isWhiteListClassification","matchedWhiteListRuleIds"]}) api_headers = {'Content-Type':'application/json'} api_response = session.request("POST", api_url, data=query, headers=api_headers) your_response = json.loads(api_response.content) print(json.dumps(your_response, indent=4, sort_keys=True))
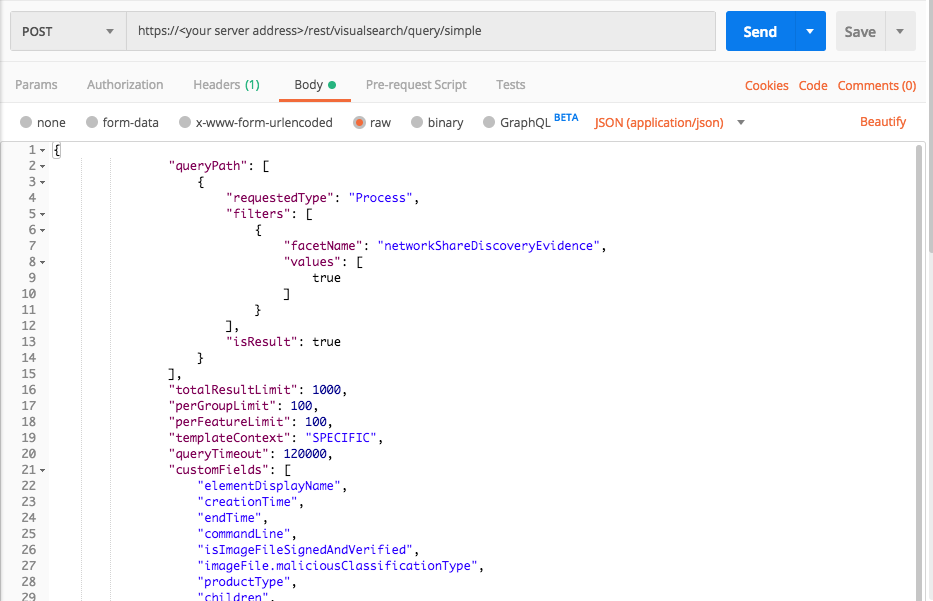
Network enumeration
Use this query to find evidence of a process performing network enumeration.
Query 1:
Request
curl --request POST \
--url https://12.34.56.78/rest/visualsearch/query/simple \
--header 'Content-Type: application/json' \
--data '{
"queryPath":[
{
"requestedType":"Process",
"filters":[
{
"facetName":"networkShareDiscoveryEvidence",
"values":[true]
}
],
"isResult":true
}
],
"totalResultLimit":1000,
"perGroupLimit":100,
"perFeatureLimit":100,
"templateContext":"SPECIFIC",
"queryTimeout":120000,
"customFields":[
"elementDisplayName",
"creationTime",
"endTime",
"commandLine",
"isImageFileSignedAndVerified",
"imageFile.maliciousClassificationType",
"productType",
"children",
"parentProcess",
"ownerMachine",
"calculatedUser",
"imageFile",
"imageFile.sha1String",
"imageFile.md5String",
"imageFile.companyName",
"imageFile.productName",
"iconBase64",
"ransomwareAutoRemediationSuspended",
"executionPrevented",
"isWhiteListClassification",
"matchedWhiteListRuleIds"
]
}'
Request
Depending on your browser settings, this linked file may open in a separate tab instead of downloading directly to your machine. If this happens, use the Save As option in your browser to save the file locally.
Use this request body:
{ "queryPath": [ { "requestedType": "Process", "filters": [ { "facetName": "networkShareDiscoveryEvidence", "values": [ true ] } ], "isResult": true } ], "totalResultLimit": 1000, "perGroupLimit": 100, "perFeatureLimit": 100, "templateContext": "SPECIFIC", "queryTimeout": 120000, "customFields": [ "elementDisplayName", "creationTime", "endTime", "commandLine", "isImageFileSignedAndVerified", "imageFile.maliciousClassificationType", "productType", "children", "parentProcess", "ownerMachine", "calculatedUser", "imageFile", "imageFile.sha1String", "imageFile.md5String", "imageFile.companyName", "imageFile.productName", "iconBase64", "ransomwareAutoRemediationSuspended", "executionPrevented", "isWhiteListClassification", "matchedWhiteListRuleIds" ] }
Request
import requests import json # Login information username = "[email protected]" password = "mypassword" server = "yourserver.com" port = "443" data = { "username": username, "password": password } headers = {"Content-Type": "application/json"} base_url = "https://" + server + ":" + port login_url = base_url + "/login.html" session = requests.session() login_response = session.post(login_url, data=data, verify=True) print (login_response.status_code) print (session.cookies.items()) # Request URL endpoint_url = "/rest/visualsearch/query/simple" api_url = base_url + endpoint_url # These are the variables that represent different fields in the request. query_element_1 = "Process" query_element_1_filter = "networkShareDiscoveryEvidence" query = json.dumps({"queryPath":[{"requestedType":query_element_1,"filters":[{"facetName":query_element_1_filter,"values":[True]}],"isResult":True}],"totalResultLimit":1000,"perGroupLimit":100,"perFeatureLimit":100,"templateContext":"SPECIFIC","queryTimeout":120000,"customFields":["elementDisplayName","creationTime","endTime","commandLine","isImageFileSignedAndVerified","imageFile.maliciousClassificationType","productType","children","parentProcess","ownerMachine","calculatedUser","imageFile","imageFile.sha1String","imageFile.md5String","imageFile.companyName","imageFile.productName","iconBase64","ransomwareAutoRemediationSuspended","executionPrevented","isWhiteListClassification","matchedWhiteListRuleIds"]}) api_headers = {'Content-Type':'application/json'} api_response = session.request("POST", api_url, data=query, headers=api_headers) your_response = json.loads(api_response.content) print(json.dumps(your_response, indent=4, sort_keys=True))
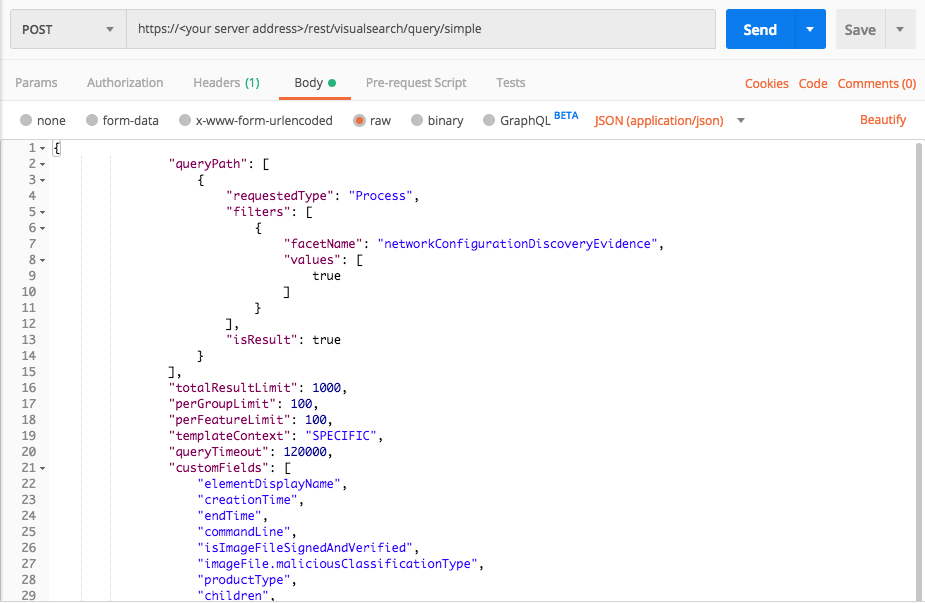
Query 2:
Request
curl --request POST \
--url https://12.34.56.78/rest/visualsearch/query/simple \
--header 'Content-Type: application/json' \
--data '{
"queryPath":[
{
"requestedType":"Process",
"filters":[
{
"facetName":"networkConfigurationDiscoveryEvidence",
"values":[true]
}
],
"isResult":true
}
],
"totalResultLimit":1000,
"perGroupLimit":100,
"perFeatureLimit":100,
"templateContext":"SPECIFIC",
"queryTimeout":120000,
"customFields":[
"elementDisplayName",
"creationTime",
"endTime",
"commandLine",
"isImageFileSignedAndVerified",
"imageFile.maliciousClassificationType",
"productType",
"children",
"parentProcess",
"ownerMachine",
"calculatedUser",
"imageFile",
"imageFile.sha1String",
"imageFile.md5String",
"imageFile.companyName",
"imageFile.productName",
"iconBase64",
"ransomwareAutoRemediationSuspended",
"executionPrevented",
"isWhiteListClassification",
"matchedWhiteListRuleIds"
]
}'
Request
Depending on your browser settings, this linked file may open in a separate tab instead of downloading directly to your machine. If this happens, use the Save As option in your browser to save the file locally.
Use this request body:
{ "queryPath": [ { "requestedType": "Process", "filters": [ { "facetName": "networkConfigurationDiscoveryEvidence", "values": [ true ] } ], "isResult": true } ], "totalResultLimit": 1000, "perGroupLimit": 100, "perFeatureLimit": 100, "templateContext": "SPECIFIC", "queryTimeout": 120000, "customFields": [ "elementDisplayName", "creationTime", "endTime", "commandLine", "isImageFileSignedAndVerified", "imageFile.maliciousClassificationType", "productType", "children", "parentProcess", "ownerMachine", "calculatedUser", "imageFile", "imageFile.sha1String", "imageFile.md5String", "imageFile.companyName", "imageFile.productName", "iconBase64", "ransomwareAutoRemediationSuspended", "executionPrevented", "isWhiteListClassification", "matchedWhiteListRuleIds" ] }
Request
Depending on your browser settings, this linked file may open in a separate tab instead of downloading directly to your machine. If this happens, use the Save As option in your browser to save the file locally.
import requests
import json
# Login information
username = "[email protected]"
password = "mypassword"
server = "yourserver.com"
port = "443"
data = {
"username": username,
"password": password
}
headers = {"Content-Type": "application/json"}
base_url = "https://" + server + ":" + port
login_url = base_url + "/login.html"
session = requests.session()
login_response = session.post(login_url, data=data, verify=True)
print (login_response.status_code)
print (session.cookies.items())
# Request URL
endpoint_url = "/rest/visualsearch/query/simple"
api_url = base_url + endpoint_url
# These are the variables that represent different fields in the request.
query_element_1 = "Process"
query_element_1_filter = "networkConfigurationDiscoveryEvidence"
query = json.dumps({"queryPath":[{"requestedType":query_element_1,"filters":[{"facetName":query_element_1_filter,"values":[True]}],"isResult":True}],"totalResultLimit":1000,"perGroupLimit":100,"perFeatureLimit":100,"templateContext":"SPECIFIC","queryTimeout":120000,"customFields":["elementDisplayName","creationTime","endTime","commandLine","isImageFileSignedAndVerified","imageFile.maliciousClassificationType","productType","children","parentProcess","ownerMachine","calculatedUser","imageFile","imageFile.sha1String","imageFile.md5String","imageFile.companyName","imageFile.productName","iconBase64","ransomwareAutoRemediationSuspended","executionPrevented","isWhiteListClassification","matchedWhiteListRuleIds"]})
api_headers = {'Content-Type':'application/json'}
api_response = session.request("POST", api_url, data=query, headers=api_headers)
your_response = json.loads(api_response.content)
print(json.dumps(your_response, indent=4, sort_keys=True))
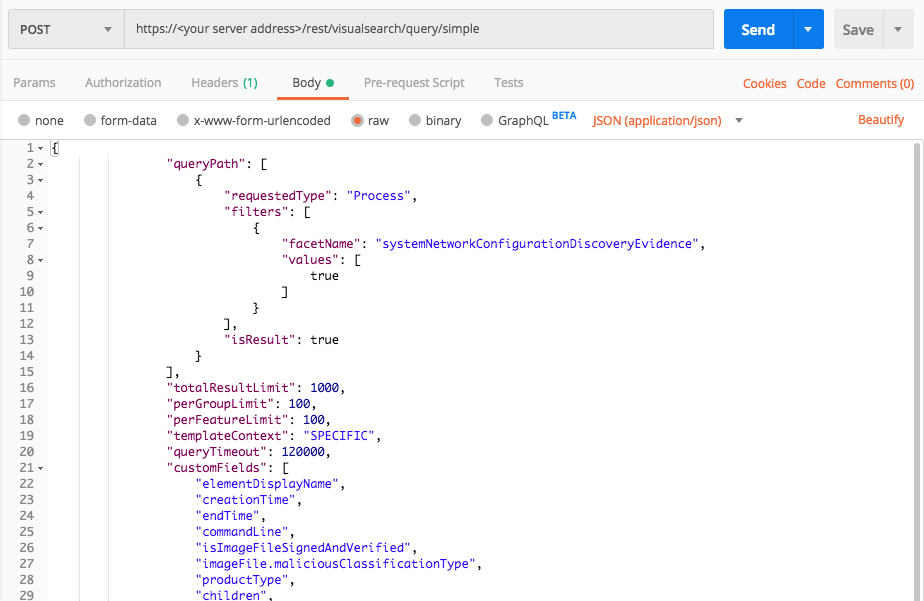
Query 3:
Request
curl --request POST \
--url https://12.34.56.78/rest/visualsearch/query/simple \
--header 'Content-Type: application/json' \
--data '{
"queryPath":[
{
"requestedType":"Process",
"filters":[
{
"facetName":"systemNetworkConfigurationDiscoveryEvidence",
"values":[true]
}
],
"isResult":true
}
],
"totalResultLimit":1000,
"perGroupLimit":100,
"perFeatureLimit":100,
"templateContext":"SPECIFIC",
"queryTimeout":120000,
"customFields":[
"elementDisplayName",
"creationTime",
"endTime",
"commandLine",
"isImageFileSignedAndVerified",
"imageFile.maliciousClassificationType",
"productType",
"children",
"parentProcess",
"ownerMachine",
"calculatedUser",
"imageFile",
"imageFile.sha1String",
"imageFile.md5String",
"imageFile.companyName",
"imageFile.productName",
"iconBase64",
"ransomwareAutoRemediationSuspended",
"executionPrevented",
"isWhiteListClassification",
"matchedWhiteListRuleIds"
]
}'
Request
Depending on your browser settings, this linked file may open in a separate tab instead of downloading directly to your machine. If this happens, use the Save As option in your browser to save the file locally.
Use this request body:
{ "queryPath": [ { "requestedType": "Process", "filters": [ { "facetName": "systemNetworkConfigurationDiscoveryEvidence", "values": [ true ] } ], "isResult": true } ], "totalResultLimit": 1000, "perGroupLimit": 100, "perFeatureLimit": 100, "templateContext": "SPECIFIC", "queryTimeout": 120000, "customFields": [ "elementDisplayName", "creationTime", "endTime", "commandLine", "isImageFileSignedAndVerified", "imageFile.maliciousClassificationType", "productType", "children", "parentProcess", "ownerMachine", "calculatedUser", "imageFile", "imageFile.sha1String", "imageFile.md5String", "imageFile.companyName", "imageFile.productName", "iconBase64", "ransomwareAutoRemediationSuspended", "executionPrevented", "isWhiteListClassification", "matchedWhiteListRuleIds" ] }
Request
Depending on your browser settings, this linked file may open in a separate tab instead of downloading directly to your machine. If this happens, use the Save As option in your browser to save the file locally.
import requests
import json
# Login information
username = "[email protected]"
password = "mypassword"
server = "yourserver.com"
port = "443"
data = {
"username": username,
"password": password
}
headers = {"Content-Type": "application/json"}
base_url = "https://" + server + ":" + port
login_url = base_url + "/login.html"
session = requests.session()
login_response = session.post(login_url, data=data, verify=True)
print (login_response.status_code)
print (session.cookies.items())
# Request URL
endpoint_url = "/rest/visualsearch/query/simple"
api_url = base_url + endpoint_url
# These are the variables that represent different fields in the request.
query_element_1 = "Process"
query_element_1_filter = "systemNetworkConfigurationDiscoveryEvidence"
query = json.dumps({"queryPath":[{"requestedType":query_element_1,"filters":[{"facetName":query_element_1_filter,"values":[True]}],"isResult":True}],"totalResultLimit":1000,"perGroupLimit":100,"perFeatureLimit":100,"templateContext":"SPECIFIC","queryTimeout":120000,"customFields":["elementDisplayName","creationTime","endTime","commandLine","isImageFileSignedAndVerified","imageFile.maliciousClassificationType","productType","children","parentProcess","ownerMachine","calculatedUser","imageFile","imageFile.sha1String","imageFile.md5String","imageFile.companyName","imageFile.productName","iconBase64","ransomwareAutoRemediationSuspended","executionPrevented","isWhiteListClassification","matchedWhiteListRuleIds"]})
api_headers = {'Content-Type':'application/json'}
api_response = session.request("POST", api_url, data=query, headers=api_headers)
your_response = json.loads(api_response.content)
print(json.dumps(your_response, indent=4, sort_keys=True))
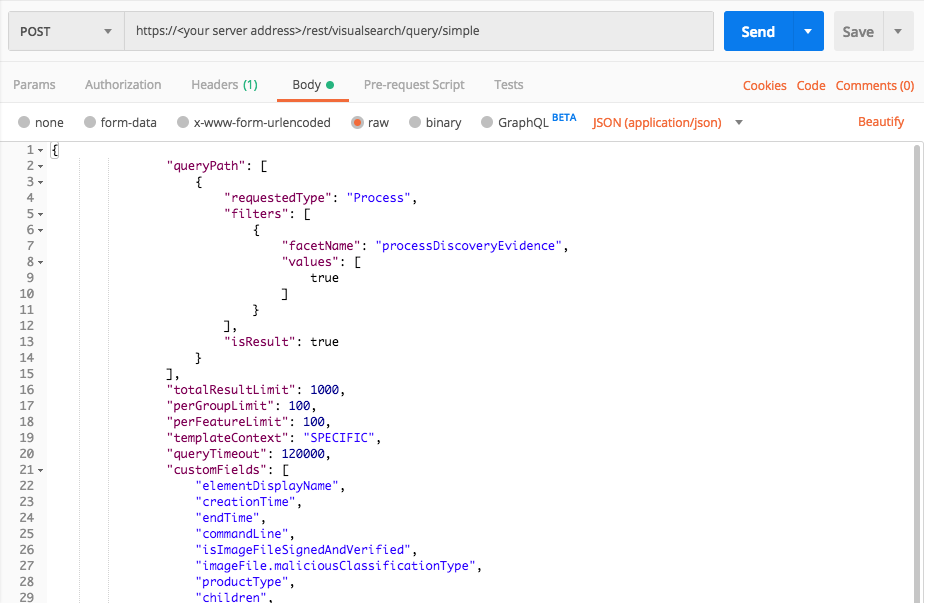
Process enumeration
Use this query to find examples of a process performing process enumeration.
Request
curl --request POST \
--url https://12.34.56.78/rest/visualsearch/query/simple \
--header 'Content-Type: application/json' \
--data '{
"queryPath":[
{
"requestedType":"Process",
"filters":[
{
"facetName":"processDiscoveryEvidence",
"values":[true]
}
],
"isResult":true
}
],
"totalResultLimit":1000,
"perGroupLimit":100,
"perFeatureLimit":100,
"templateContext":"SPECIFIC",
"queryTimeout":120000,
"customFields":[
"elementDisplayName",
"creationTime",
"endTime",
"commandLine",
"isImageFileSignedAndVerified",
"imageFile.maliciousClassificationType",
"productType",
"children",
"parentProcess",
"ownerMachine",
"calculatedUser",
"imageFile",
"imageFile.sha1String",
"imageFile.md5String",
"imageFile.companyName",
"imageFile.productName",
"iconBase64",
"ransomwareAutoRemediationSuspended",
"executionPrevented",
"isWhiteListClassification",
"matchedWhiteListRuleIds"
]
}'
Request
Depending on your browser settings, this linked file may open in a separate tab instead of downloading directly to your machine. If this happens, use the Save As option in your browser to save the file locally.
Use this request:
{ "queryPath": [ { "requestedType": "Process", "filters": [ { "facetName": "processDiscoveryEvidence", "values": [ true ] } ], "isResult": true } ], "totalResultLimit": 1000, "perGroupLimit": 100, "perFeatureLimit": 100, "templateContext": "SPECIFIC", "queryTimeout": 120000, "customFields": [ "elementDisplayName", "creationTime", "endTime", "commandLine", "isImageFileSignedAndVerified", "imageFile.maliciousClassificationType", "productType", "children", "parentProcess", "ownerMachine", "calculatedUser", "imageFile", "imageFile.sha1String", "imageFile.md5String", "imageFile.companyName", "imageFile.productName", "iconBase64", "ransomwareAutoRemediationSuspended", "executionPrevented", "isWhiteListClassification", "matchedWhiteListRuleIds" ] }
Request
Depending on your browser settings, this linked file may open in a separate tab instead of downloading directly to your machine. If this happens, use the Save As option in your browser to save the file locally.
import requests import json # Login information username = "[email protected]" password = "mypassword" server = "yourserver.com" port = "443" data = { "username": username, "password": password } headers = {"Content-Type": "application/json"} base_url = "https://" + server + ":" + port login_url = base_url + "/login.html" session = requests.session() login_response = session.post(login_url, data=data, verify=True) print (login_response.status_code) print (session.cookies.items()) # Request URL endpoint_url = "/rest/visualsearch/query/simple" api_url = base_url + endpoint_url # These are the variables that represent different fields in the request. query_element_1 = "Process" query_element_1_filter = "processDiscoveryEvidence" query = json.dumps({"queryPath":[{"requestedType":query_element_1,"filters":[{"facetName":query_element_1_filter,"values":[True]}],"isResult":True}],"totalResultLimit":1000,"perGroupLimit":100,"perFeatureLimit":100,"templateContext":"SPECIFIC","queryTimeout":120000,"customFields":["elementDisplayName","creationTime","endTime","commandLine","isImageFileSignedAndVerified","imageFile.maliciousClassificationType","productType","children","parentProcess","ownerMachine","calculatedUser","imageFile","imageFile.sha1String","imageFile.md5String","imageFile.companyName","imageFile.productName","iconBase64","ransomwareAutoRemediationSuspended","executionPrevented","isWhiteListClassification","matchedWhiteListRuleIds"]}) api_headers = {'Content-Type':'application/json'} api_response = session.request("POST", api_url, data=query, headers=api_headers) your_response = json.loads(api_response.content) print(json.dumps(your_response, indent=4, sort_keys=True))
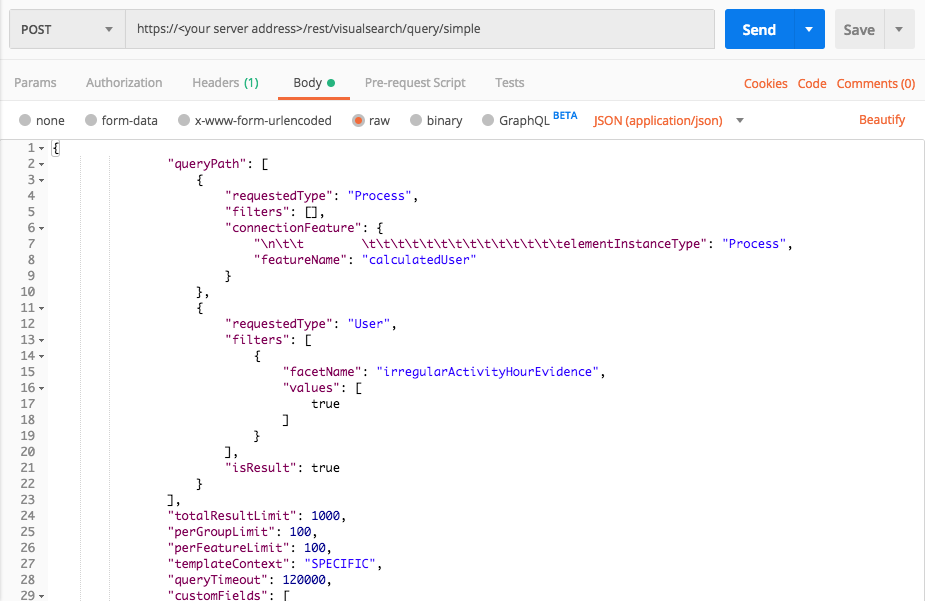
Abnormal hour activity
Use these queries to find evidence of abnormal hour activities by users.
Query 1:
Request
curl --request POST \
--url https://12.34.56.78/rest/visualsearch/query/simple \
--header 'Content-Type: application/json' \
--data '{
"queryPath":[
{
"requestedType":"Process",
"filters":[],
"connectionFeature": {"
elementInstanceType":"Process",
"featureName":"calculatedUser"
}
},
{
"requestedType":"User",
"filters":[
{
"facetName":"irregularActivityHourEvidence",
"values":[true]
}
],
"isResult":true
}
],
"totalResultLimit":1000,
"perGroupLimit":100,
"perFeatureLimit":100,
"templateContext":"SPECIFIC",
"queryTimeout":120000,
"customFields":[
"domain",
"ownerMachine",
"ownerOrganization.name",
"isLocalSystem",
"elementDisplayName"
]
}'
Request
Depending on your browser settings, this linked file may open in a separate tab instead of downloading directly to your machine. If this happens, use the Save As option in your browser to save the file locally.
Use this request body:
{ "queryPath": [ { "requestedType": "Process", "filters": [], "connectionFeature": { "\n\t\t \t\t\t\t\t\t\t\t\t\t\t\t\t\telementInstanceType": "Process", "featureName": "calculatedUser" } }, { "requestedType": "User", "filters": [ { "facetName": "irregularActivityHourEvidence", "values": [ true ] } ], "isResult": true } ], "totalResultLimit": 1000, "perGroupLimit": 100, "perFeatureLimit": 100, "templateContext": "SPECIFIC", "queryTimeout": 120000, "customFields": [ "domain", "ownerMachine", "ownerOrganization.name", "isLocalSystem", "elementDisplayName" ] }
Request
Depending on your browser settings, this linked file may open in a separate tab instead of downloading directly to your machine. If this happens, use the Save As option in your browser to save the file locally.
import requests import json # Login information username = "[email protected]" password = "mypassword" server = "yourserver.com" port = "443" data = { "username": username, "password": password } headers = {"Content-Type": "application/json"} base_url = "https://" + server + ":" + port login_url = base_url + "/login.html" session = requests.session() login_response = session.post(login_url, data=data, verify=True) print (login_response.status_code) print (session.cookies.items()) # Request URL endpoint_url = "/rest/visualsearch/query/simple" api_url = base_url + endpoint_url # These are the variables that represent different fields in the request. query_element_1 = "Process" linking_element = "Process" linking_feature = "calculatedUser" query_element_2 = "User" query_element_2_filter = "irregularActivityHourEvidence" query = json.dumps({"queryPath":[{"requestedType":query_element_1,"filters":[],"connectionFeature":{"elementInstanceType":linking_element,"featureName":linking_feature}},{"requestedType":query_element_2,"filters":[{"facetName":query_element_2_filter,"values":[True]}],"isResult":True}],"totalResultLimit":1000,"perGroupLimit":100,"perFeatureLimit":100,"templateContext":"SPECIFIC","queryTimeout":120000,"customFields":["domain","ownerMachine","ownerOrganization.name","isLocalSystem","elementDisplayName"]}) api_headers = {'Content-Type':'application/json'} api_response = session.request("POST", api_url, data=query, headers=api_headers) your_response = json.loads(api_response.content) print(json.dumps(your_response, indent=4, sort_keys=True))
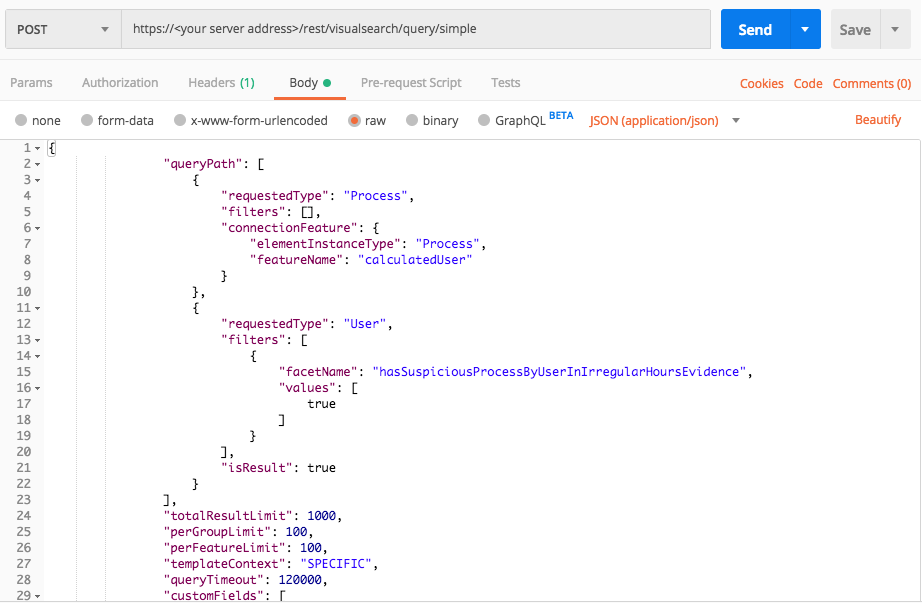
Query 2:
Request
curl --request POST \
--url https://12.34.56.78/rest/visualsearch/query/simple \
--header 'Content-Type: application/json' \
--data '{
"queryPath":[
{
"requestedType":"Process",
"filters":[],
"connectionFeature": {
"elementInstanceType":"Process",
"featureName":"calculatedUser"
}
},
{
"requestedType":"User",
"filters":[
{
"facetName":"hasSuspiciousProcessByUserInIrregularHoursEvidence",
"values":[true]
}
],
"isResult":true
}
],
"totalResultLimit":1000,
"perGroupLimit":100,
"perFeatureLimit":100,
"templateContext":"SPECIFIC",
"queryTimeout":120000,
"customFields":[
"domain",
"ownerMachine",
"ownerOrganization.name",
"isLocalSystem",
"elementDisplayName"
]
}'
Request
Depending on your browser settings, this linked file may open in a separate tab instead of downloading directly to your machine. If this happens, use the Save As option in your browser to save the file locally.
Use this request body:
{ "queryPath": [ { "requestedType": "Process", "filters": [], "connectionFeature": { "elementInstanceType": "Process", "featureName": "calculatedUser" } }, { "requestedType": "User", "filters": [ { "facetName": "hasSuspiciousProcessByUserInIrregularHoursEvidence", "values": [ true ] } ], "isResult": true } ], "totalResultLimit": 1000, "perGroupLimit": 100, "perFeatureLimit": 100, "templateContext": "SPECIFIC", "queryTimeout": 120000, "customFields": [ "domain", "ownerMachine", "ownerOrganization.name", "isLocalSystem", "elementDisplayName" ] }
Request
Depending on your browser settings, this linked file may open in a separate tab instead of downloading directly to your machine. If this happens, use the Save As option in your browser to save the file locally.
import requests import json # Login information username = "[email protected]" password = "mypassword" server = "yourserver.com" port = "443" data = { "username": username, "password": password } headers = {"Content-Type": "application/json"} base_url = "https://" + server + ":" + port login_url = base_url + "/login.html" session = requests.session() login_response = session.post(login_url, data=data, verify=True) print (login_response.status_code) print (session.cookies.items()) # Request URL endpoint_url = "/rest/visualsearch/query/simple" api_url = base_url + endpoint_url # These are the variables that represent different fields in the request. query_element_1 = "Process" linking_element = "Process" linking_feature = "calculatedUser" query_element_2 = "User" query_element_2_filter = "hasSuspiciousProcessByUserInIrregularHoursEvidence" query = json.dumps({"queryPath":[{"requestedType":query_element_1,"filters":[],"connectionFeature":{"elementInstanceType":linking_element,"featureName":linking_feature}},{"requestedType":query_element_2,"filters":[{"facetName":query_element_2_filter,"values":[True]}],"isResult":True}],"totalResultLimit":1000,"perGroupLimit":100,"perFeatureLimit":100,"templateContext":"SPECIFIC","queryTimeout":120000,"customFields":["domain","ownerMachine","ownerOrganization.name","isLocalSystem","elementDisplayName"]}) api_headers = {'Content-Type':'application/json'} api_response = session.request("POST", api_url, data=query, headers=api_headers) your_response = json.loads(api_response.content) print(json.dumps(your_response, indent=4, sort_keys=True))