Retrieve a List of MalOp Detection Types
Endpoint URL: https://<your server>/rest/v2/customRules/getMalopDetectionTypes
Endpoint URI: /v2/customRules/getMalopDetectionTypes
Action: GET
Returns a list of all available detection types you can use for the custom detection rule.
Note
Ensure that you have logged into the Cybereason platform. For details, see Log in with the API.
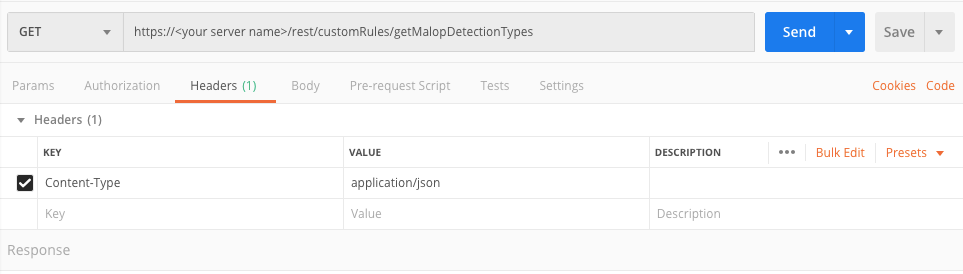
Request Headers
You must add an Content-Type:application/json header with the request.
Note
If you are using cURL, add the authorization cookie details or the path to the file with cookie details with every request.
Request Body
None
Request Parameters
URL/URI parameters: none
Request Body Parameters: none
Response Status Codes
This request can return the following status codes:
200: Success OK
Response Success Schema
The response includes a list of the supported detection types for any generated Malop:
Field |
Type |
Description |
|---|---|---|
enumName |
Enum |
The possible values for the detection type used in a generated Malop. The possible values for this field vary:
|
translation |
String |
The Cybereason platform name for the detection type. |
Response Failure Schema
None
Important Response Fields
Important information is found in these fields:
enumName parameter: The unique value the Cybereason platform users for the detection types.
translation parameter: The Cybereason platform name for the detection type.
Example: Get a list of available detection types
Request
curl --request GET \
--url https://12.34.56.78/rest/v2/customRules/getMalopDetectionTypes \
--header 'Content-Type:application/json' \
Response
[
{
"enumName":"KNOWN_MALWARE",
"translation":"Known malware"
},
{
"enumName":"MALICIOUS_PROCESS",
"translation":"Malicious Process"
},
{
"enumName":"PUP",
"translation":"PUP"
},
{
"enumName":"CNC",
"translation":"Command and Control"
},
{
"enumName":"RECONNAISSANCE",
"translation":"Reconnaissance"
},
{
"enumName":"EXTENSION_MANIPULATION",
"translation":"Extension manipulation"
},
{
"enumName":"PROCESS_INJECTION",
"translation":"Process injection"
},
{
"enumName":"PERSISTENCE",
"translation":"Persistence"
},
{
"enumName":"ELEVATED_ACCESS",
"translation":"Elevated access"
},
{
"enumName":"PHISHING",
"translation":"Phishing"
},
{
"enumName":"DATA_TRANSMISSION_VOLUME",
"translation":"Data transmission volume"
},
{
"enumName":"CREDENTIAL_THEFT",
"translation":"Credential theft"
},
{
"enumName":"LATERAL_MOVEMENT",
"translation":"Lateral Movement"
},
{
"enumName":"RANSOMWARE",
"translation":"Ransomware"
},
{
"enumName":"BLACKLIST",
"translation":"Blacklist"
},
{
"enumName":"CUSTOM_RULE",
"translation":"Custom rule"
},
{
"enumName":"UNAUTHORIZED_USER",
"translation":"Compromised user"
}
]
Request
Use this request body:
Response
[
{
"enumName":"KNOWN_MALWARE",
"translation":"Known malware"
},
{
"enumName":"MALICIOUS_PROCESS",
"translation":"Malicious Process"
},
{
"enumName":"PUP",
"translation":"PUP"
},
{
"enumName":"CNC",
"translation":"Command and Control"
},
{
"enumName":"RECONNAISSANCE",
"translation":"Reconnaissance"
},
{
"enumName":"EXTENSION_MANIPULATION",
"translation":"Extension manipulation"
},
{
"enumName":"PROCESS_INJECTION",
"translation":"Process injection"
},
{
"enumName":"PERSISTENCE",
"translation":"Persistence"
},
{
"enumName":"ELEVATED_ACCESS",
"translation":"Elevated access"
},
{
"enumName":"PHISHING",
"translation":"Phishing"
},
{
"enumName":"DATA_TRANSMISSION_VOLUME",
"translation":"Data transmission volume"
},
{
"enumName":"CREDENTIAL_THEFT",
"translation":"Credential theft"
},
{
"enumName":"LATERAL_MOVEMENT",
"translation":"Lateral Movement"
},
{
"enumName":"RANSOMWARE",
"translation":"Ransomware"
},
{
"enumName":"BLACKLIST",
"translation":"Blacklist"
},
{
"enumName":"CUSTOM_RULE",
"translation":"Custom rule"
},
{
"enumName":"UNAUTHORIZED_USER",
"translation":"Compromised user"
}
]
Request
Depending on your browser settings, this linked file may open in a separate tab instead of downloading directly to your machine. If this happens, use the Save As option in your browser to save the file locally.
import requests
import json
# Login information
username = "[email protected]"
password = "mypassword"
server = "yourserver.com"
port = "443"
data = {
"username": username,
"password": password
}
headers = {"Content-Type": "application/json"}
base_url = "https://" + server + ":" + port
login_url = base_url + "/login.html"
session = requests.session()
login_response = session.post(login_url, data=data, verify=True)
print (login_response.status_code)
print (session.cookies.items())
# Request URL
endpoint_url = "/rest/v2/customRules/getMalopDetectionTypes"
api_url = base_url + endpoint_url
api_headers = {'Content-Type':'application/json'}
api_response = session.request("GET", api_url, headers=api_headers)
your_response = json.loads(api_response.content)
print(json.dumps(your_response, indent=4, sort_keys=True))
Response
[
{
"enumName":"KNOWN_MALWARE",
"translation":"Known malware"
},
{
"enumName":"MALICIOUS_PROCESS",
"translation":"Malicious Process"
},
{
"enumName":"PUP",
"translation":"PUP"
},
{
"enumName":"CNC",
"translation":"Command and Control"
},
{
"enumName":"RECONNAISSANCE",
"translation":"Reconnaissance"
},
{
"enumName":"EXTENSION_MANIPULATION",
"translation":"Extension manipulation"
},
{
"enumName":"PROCESS_INJECTION",
"translation":"Process injection"
},
{
"enumName":"PERSISTENCE",
"translation":"Persistence"
},
{
"enumName":"ELEVATED_ACCESS",
"translation":"Elevated access"
},
{
"enumName":"PHISHING",
"translation":"Phishing"
},
{
"enumName":"DATA_TRANSMISSION_VOLUME",
"translation":"Data transmission volume"
},
{
"enumName":"CREDENTIAL_THEFT",
"translation":"Credential theft"
},
{
"enumName":"LATERAL_MOVEMENT",
"translation":"Lateral Movement"
},
{
"enumName":"RANSOMWARE",
"translation":"Ransomware"
},
{
"enumName":"BLACKLIST",
"translation":"Blacklist"
},
{
"enumName":"CUSTOM_RULE",
"translation":"Custom rule"
},
{
"enumName":"UNAUTHORIZED_USER",
"translation":"Compromised user"
}
]